Details of an eight-year-old security vulnerability in the Linux kernel have emerged that the researchers say is “as nasty as Dirty Pipe.”
Dubbed DirtyCred by a group of academics from Northwestern University, the security weakness exploits a previously unknown flaw (CVE-2022-2588) to escalate privileges to the maximum level.
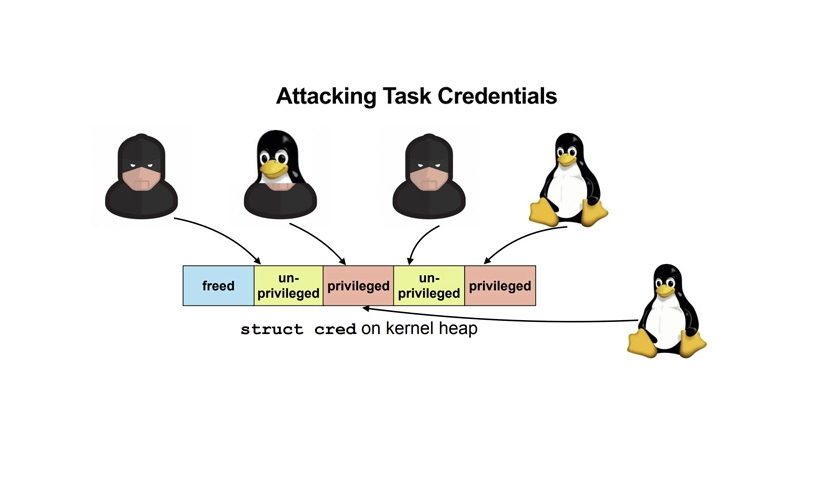
“DirtyCred is a kernel exploitation concept that swaps unprivileged kernel credentials with privileged ones to escalate privilege,” researchers Zhenpeng Lin, Yuhang Wu, and Xinyu Xing noted. “Instead of overwriting any critical data fields on kernel heap, DirtyCred abuses the heap memory reuse mechanism to get privileged.”
This entails three steps –
Free an in-use unprivileged credential with the vulnerability
Allocate privileged credentials in the freed memory slot by triggering a privileged userspace process such as su, mount, or sshd
Operate as a privileged user
The novel exploitation method, according to the researchers, pushes the dirty pipe to the next level, making it more general as well as potent in a manner that could work on any version of the affected kernel.
Read more: thehackernews.com